You're reading an older article from ELECTRICAL CONTRACTOR. Some content, such as code-related information, may be outdated. Visit our homepage to view the most up-to-date articles.
There have been articles in magazines and on websites concerning the vulnerability of the smart grid and, in particular, smart meters. These articles contain some truth and a lot of fiction. One of the biggest scares is about the ability to turn loads on and off and bring the grid down, which would actually be a rather “dumb” function for the meter to just follow information sent to it without any regard to its content or validity. Rather than continuing to spread more rumors, this article focuses on what is being done in the industry with regard to security of smart meters, though even the definition of a “smart meter” is somewhat nebulous.
Let’s go back to Title XIII—Smart Grid of the Energy Independence and Security Act of 2007 (EISA). The term “security” shows up in just about every section, as well as the title itself. Section 1301, Statement of Policy on Modernization of the Electricity Grid, lists characteristics of the smart grid, the first two being the increased use of digital information and controls technology to improve reliability, security and efficiency of the electric grid and the dynamic optimization of grid operations and resources, with full cybersecurity.
Section 1303, Smart Grid Advisory Committee and Smart Grid Task Force, has written in its Advisory Committee mission statement, “the evolution of widely accepted technical and practical standards and protocols to allow interoperability and inter-communication among smart-grid capable devices” in addition to “development of widely accepted smart-grid standards and protocols.” Programs called out by Section 1304, Smart Grid Technology Research, Development, and Demonstration, include ones to “conduct research to advance the use of wide-area measurement and control networks, including data mining, visualization, advanced computing, and secure and dependable communications in a highly distributed environment.”
But what progress has been made toward these secure communications? There is significant movement within the various smart grid groups to improve security for meters, relays and all of the other equipment that will eventually be part of the smart grid. It is not in place yet partially because it is known that the security issue must be addressed. Contracts have been awarded to do the initial legwork and to form committees within the standards-making groups, which will eventually require a peer-review and balloting process of the standards. The recently published IEC 62351, “Power System Control and Associated Communications—Data and Communication Security,” standard will likely serve as the basis for the communications between equipment used in the smart grid. IEC 62351 defines “security requirements for power system management and information exchange, including communications network and system security issues, TCP/IP and MMS profiles, and security for Inter-Control Center Protocol and Sub-station automation and protection.”
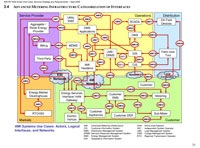
This task is not easy. The National Institute of Standards and Technology (NIST) was awarded $10 million from the American Recovery and Reinvestment Act to carry out some of those responsibilities listed under the EISA. The NIST Cyber Security Coordination Task Group recently produced a 237-page draft report, “Smart Grid Cyber Security, Strategy and Requirements,” which demonstrates, in the chart below, just how many interface types will be involved in such, all of which must be secure, reliable and efficient.
So in the meantime, while this is being worked out, just sit back and relax, let the historically cautious-and-slow-to-adopt-new-electric-power industry work with the cybersecurity experts to eventually incorporate EISA 2007 smart grid and smart meter technologies without jeopardizing your privacy, the grid’s stability or the utilities’ revenue stream. Your electrons and their money, since a smart meter is really like a digital cash register for them, will soon be secure.
BINGHAM, a contributing editor for power quality, can be reached at 732.287.3680.
About The Author
BINGHAM, a contributing editor for power quality, can be reached at 908.499.5321.